



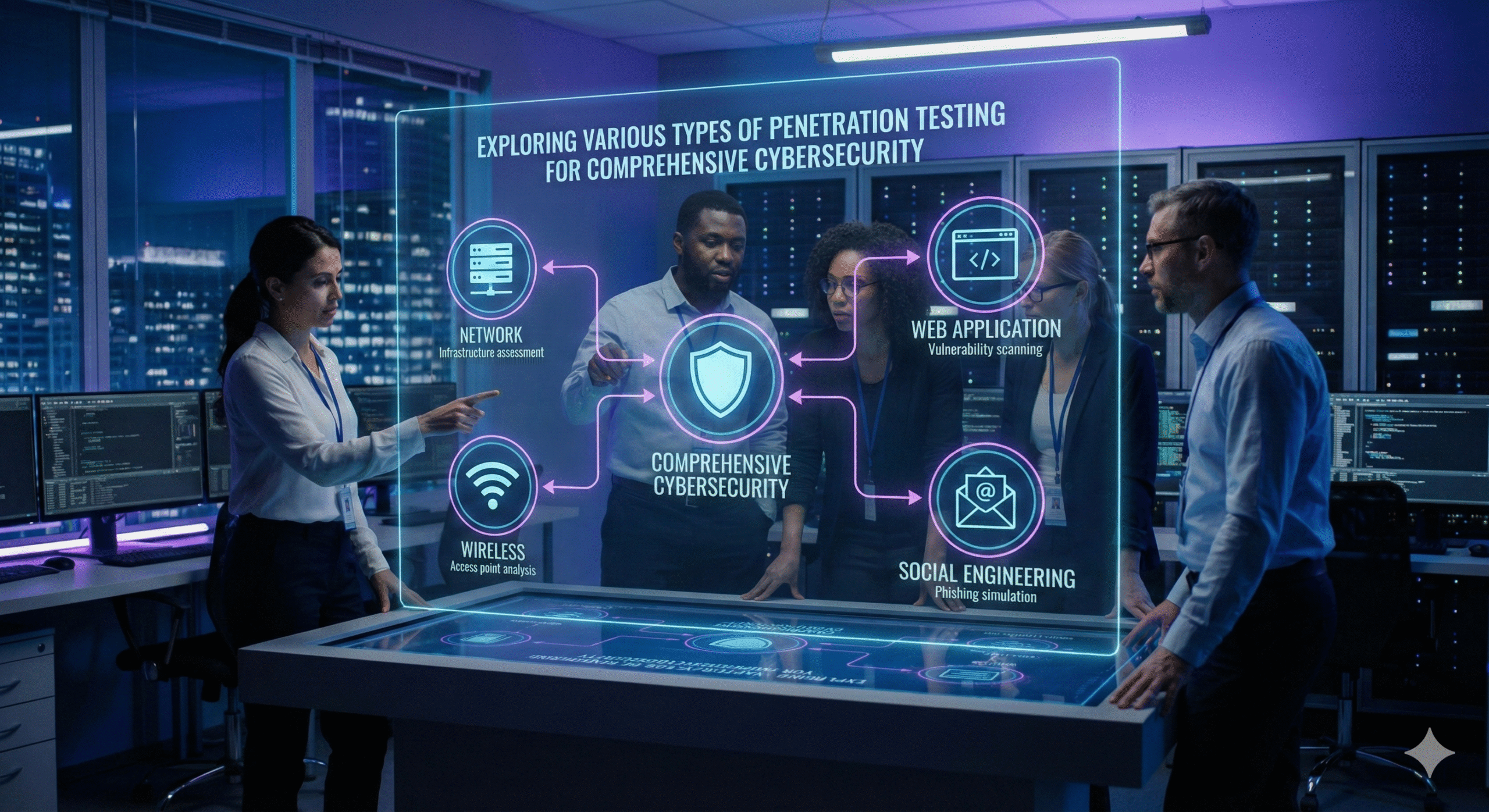
Cyber security experts understand the threat of cyber-attacks exists now more than ever. As businesses undergo digitalization of their processes and procedures penetration testing and checking their systems for weaknesses becomes crucial. Penetration testing methodology helps experts find flaws and gaps within the applications, networks, and systems. By simulating the real-world attacks pen testing allows experts to secure organizations from these attack vectors. Keep reading to understand all the different types of penetration testing.
Penetration tests are mainly divided into two broad categories depending upon:
Black Box Testing
As the name suggests, black box testing is done to test the target system against external threats. In this methodology, the ethical hacker doesn’t know anything about the system/application. Hacker does external enumeration and exploits the system as an external attacker would.
Black box testing gives an accurate depiction of attacks from real-world hackers.
Some of the other benefits of black box testing are:
White Box Testing
White box testing, also known as glass box testing. In this testing methodology, the hacker is given everything there is to know about the system. Whitebox testing means performing tests from a developer’s perspective.
White Box Testing
Some Benefits of white box testing are :
Grey Box Testing
Grey box testing falls in between white and black box testing. Sometimes referred to as translucent box testing. In this type of testing, partial information about the application is known to the tester.
The Grey box testing methodology can
Grey box testing can
Network Penetration Testing
Network penetration testing includes all the tests that are conducted around the organization’s network.
Network penetration testing includes tests around.
Benefits of network Penetration Testing include but are not limited to:
Application Penetration Testing
Application penetration testing includes tests performed to validate the security of web applications. These tests include but are not limited to testing the application’s mainframe which includes ActiveX, Silverlight, javaApplets, APIs, etc.
Why perform Application Penetration Testing?
Wireless Penetration Testing
Wireless Penetration Testing consists of tests performed around all wireless devices used within your organization. These devices include but are not limited to Laptops, tablets, cell phones.
Includes but not limited to.
Why you should perform Wireless Penetration Testing
Social Engineering Penetration Testing
This type of penetration testing is performed by tricking employees into giving out sensitive information. Most times it includes the employees password or some other confidential data. The human factor is the weakest link in any security program.
Social engineering Tests include
Remote
Involves tricking an employee to give away sensitive information over electronic means.
Physical
Involves the gathering of sensitive information through physical means such as following an employee into there workspace or blackmailing them.
You should perform Social Engineering penetration Tests because
Client-Side Penetration Testing
This testing methodology consists of tests against software installed on the client’s workstations. These tests include but are not limited to.
Web Browsers. (Chrome, Firefox, Safari)
Content Creation Softwares. (Adobe FrameMaker, RoboHelp etc.)
Media Players
Why you should perform Client Side Penetration Testing
Now that you know all the different types of penetration testing it’s time to get started testing. Contacting a professional penetration testing company will allow you to have someone walk you through your options. Here at Cyber Security Hive we offer professional services at affordable prices. We have the expertise and tools to help businesses of all sizes improve their security posture.
Understanding Vulnerabilities for Penetration Testing
Pen Test Process – The steps to performing a Pen Test
Top 5 Cyber Security Careers (With Salary Trends)
Certified Ethical Hacker (CEH) Certification Guide
Offensive Security Certified Expert (OSCE) Certification Guide