



Penetration testing (also known as pen-testing) is the process of scanning a computer network, application, or system for exploitable vulnerabilities. Vulnerabilities are gaps or weaknesses in your security that could be leveraged by malicious hackers to compromise your systems.
Hackers use penetration testing techniques to hack into systems and networks to steal sensitive data and learn how they can improve their hacking skills. Ethical hackers, also known as pen testers, conduct penetration tests using manual methods and automated pen-testing tools to identify security gaps.
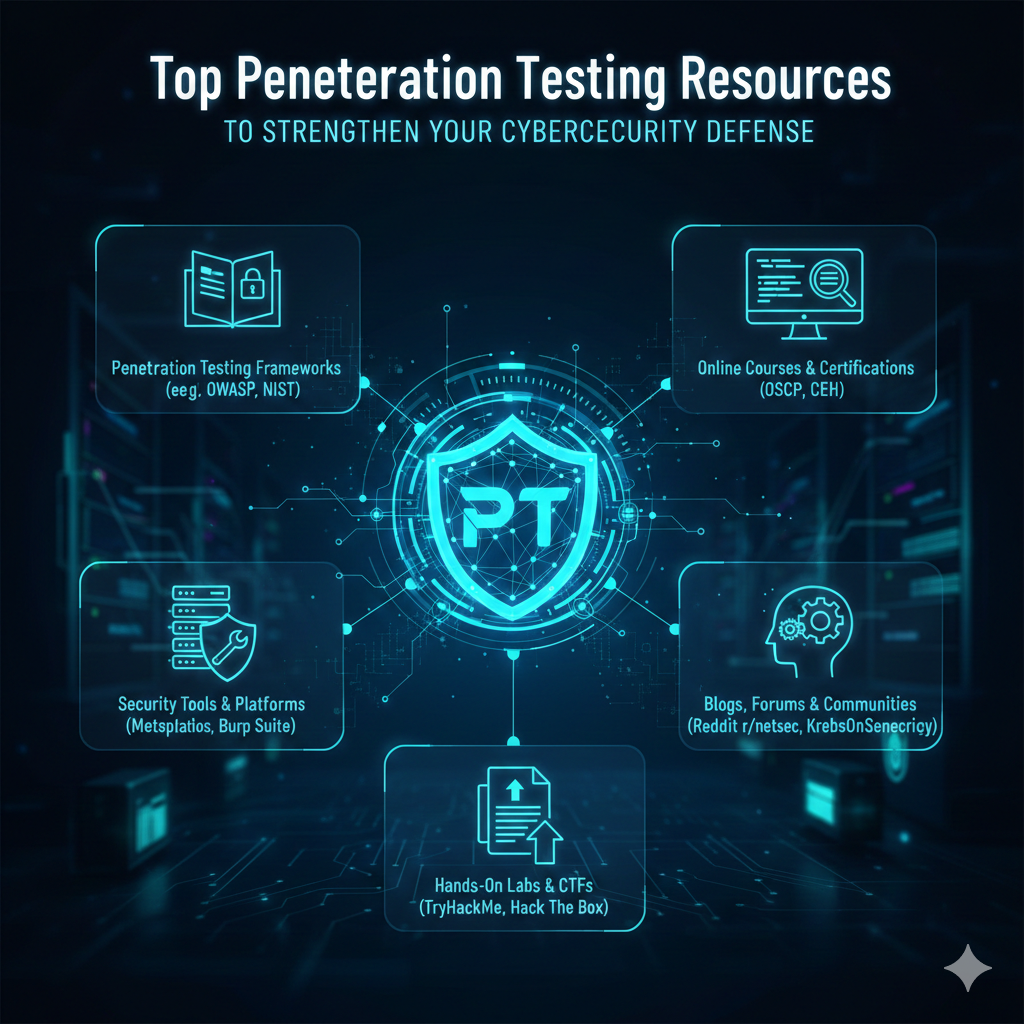
In this guide, we’ll introduce you to some of the most effective penetration testing tools.
Just like hackers, penetration testers use a variety of hacking tools and techniques to test a company’s security defenses.
However, unlike malicious hackers, pen testers operate with permission from the organization and aim to highlight weaknesses in security before the bad guys can detect and exploit them.
Let’s take a look at some of the reasons why penetration testing is important to your organization.
Penetration testing uncovers vulnerabilities in your security defenses that could be leveraged by hackers.
Data breaches are expensive, costing businesses an average of $3.92 million per incident. Regular penetration testing can help you prevent data breaches before they happen.
Running regular penetration tests is one of the most effective ways to meet various cybersecurity compliance requirements such as GDPR, PCI DSS, and ISO 27001.
Penetration tests allow you to see how an attacker would exploit system vulnerabilities in real-time and what kind of damage they can cause to your business.
Ideally, you should perform penetration tests on your network and applications regularly to ensure they don’t contain any exploitable vulnerabilities. However, this also depends on your specific industry requirements and any applicable compliance regulations.
Penetration testers use a wide range of hacking tools to scan networks, systems, and applications for vulnerabilities. Below are some of the most useful categories of penetration testing tools.
A port scanner is a computer program that tests computer network ports to determine whether they are open and vulnerable to exploitation.
Penetration testers often rely on port scanning tools to create an attack map they can use to identify vulnerabilities in your systems.
The top Port Scanner Tools:
Nmap
Zenmap
Vulnerability scanners automate the process of scanning your systems and networks for known security vulnerabilities.
Here are the best vulnerability scanner tools:
Nessus Professional
OpenVAS
Packet sniffers allow pen testers to intercept and capture network traffic in real-time. The below tool is the best network sniffing tool out there:
Wireshark
Password cracking tools are used to uncover passwords or learn how strong your company’s password policies are by using various hacking techniques.
Here are common password cracking tools and techniques:
Dictionary Attacks
Brute Force Attacks
Hybrid Attacks
Let’s dive into each tool and learn more about what they do.
Whether you’re a beginner or advanced pen tester, these tools will be essential to your penetration testing efforts.
Nmap (“Network Mapper”) is a free and open-source tool used for network discovery and security auditing. Penetration testers and cyber security professionals use Nmap to scan large networks using the ping sweep command.
Below are some key features of Nmap:
Scans large networks quickly
Detects what operating systems are running on remote devices
Identifies what ports are available and the services that those ports offer
Nessus Professional is a vulnerability scanner developed by Tenable. The software allows you to scan networks and applications for known vulnerabilities and generate detailed reports based on your findings.
Key Features of Nessus Professional:
Fast and consistent vulnerability scanner
Includes remediation guidance and risk ratings for vulnerabilities
Run both local and remote scans
Wireshark is considered by many to be the best network sniffer currently available. Packet sniffing tools like Wireshark allow pen testers to capture packets and analyze network traffic as it’s happening.
Wireshark Key Features:
Real-time traffic analysis
Packet decoding with rich and color-coded information
Supports hundreds of protocols
Burp Suite is a piece of computer software used primarily for security testing of web applications. Burp Suite is an integrated platform that comes bundled with various tools that are designed to work seamlessly together.
Key Features of Burp Suite:
Simple user interface with automated powerful tools
Advanced web crawling and spidering capabilities
Identifies vulnerabilities and offers suggestions on how to fix them
Here are some recommended best practices that you can follow to perform successful penetration tests:
Set clear objectives and scope: Both you and the pen tester should know what’s being tested and what you hope to accomplish with the penetration test. Determine your objectives before kicking off the test.
Test regularly: It’s important to test regularly so new vulnerabilities can be detected and resolved promptly.
Use both automated and manual testing techniques: Automated penetration testing tools can significantly speed up the testing process. However, manual testing is required to identify complex vulnerabilities that automated scanners often miss. Ideally, you should use both types of testing.
Have proper authorization: Never perform a penetration test without having written approval from a governing authority. While it’s done with good intentions, hacking into a network without permission is illegal.
Penetration testing is one of the most important steps you can take to secure your IT infrastructure and ensure compliance with industry regulations. The tools listed above are some of the most popular penetration testing tools used by cyber security professionals.
Take advantage of these tools to perform thorough penetration tests and keep your networks and applications safe from cybercriminals.
If you’re searching for reliable penetration testing services for your business, look no further than Cyber Security Hive. We’re a globally distributed cybersecurity company that provides penetration testing services in the US, India, UAE, and Dubai. Contact us today!