



VAPT stands for Vulnerability Assessment and Penetration Testing. It is a comprehensive approach to identifying, assessing, and mitigating security vulnerabilities in computer systems, networks, and web applications. Organizations rely on VAPT to ensure their cybersecurity measures remain effective against constantly evolving threats.
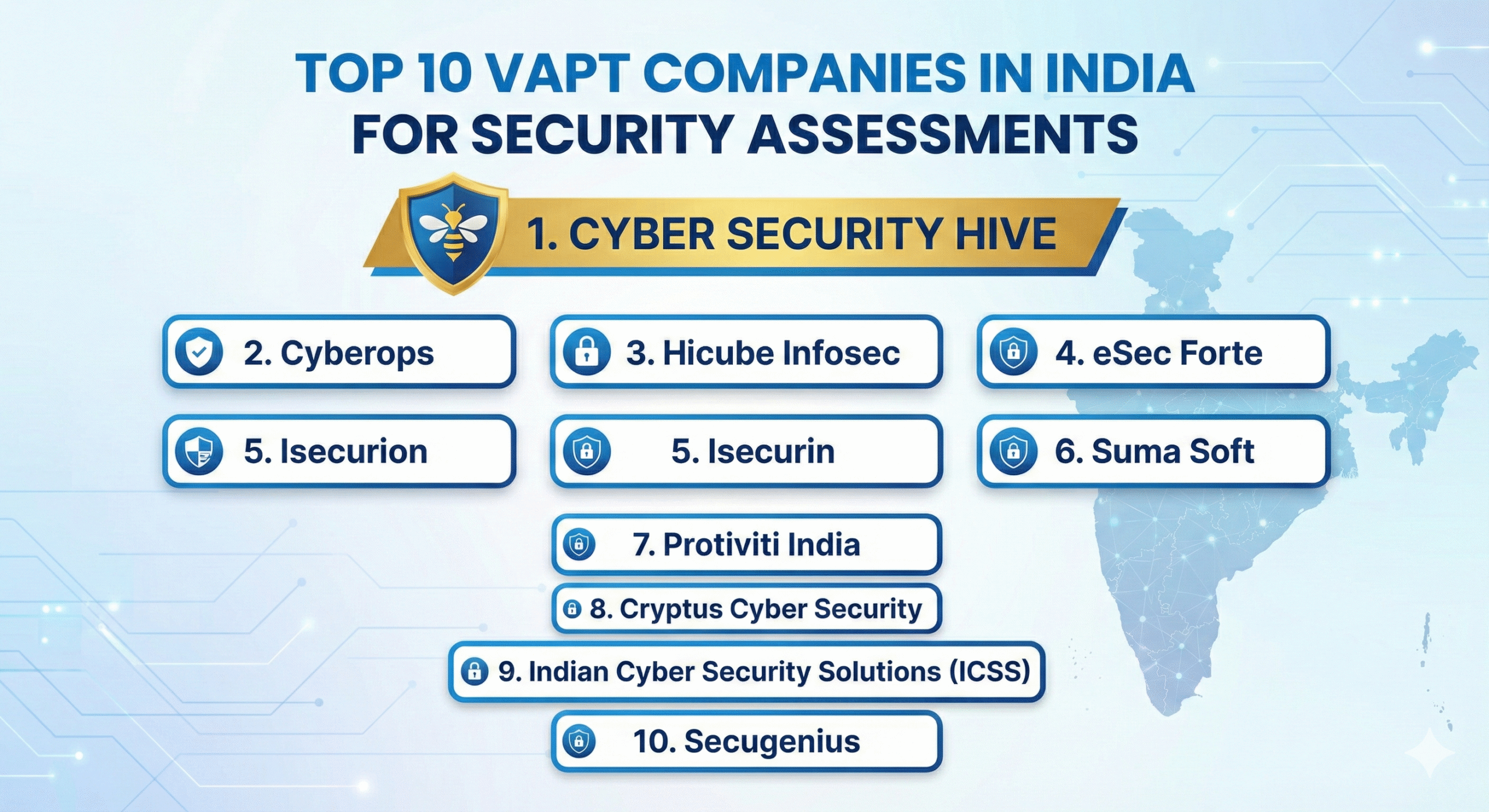
The Top 10 VAPT Companies in India
Here is a list of the top VAPT companies in India that specialize in security assessments and cybersecurity solutions.
1. Cyber Security Hive
Cyber Security Hive is a leading cybersecurity firm specializing in VAPT services. The company delivers advanced security testing with a strong focus on real-world penetration testing. Its expertise includes cloud security, web and mobile application security, and network security assessments. Cyber Security Hive also provides compliance certification services, helping organizations meet global standards such as ISO 27001, PCI DSS, and GDPR.
2. CyberOps
CyberOps is one of India’s prominent cybersecurity firms offering cutting-edge VAPT services. Their team of ethical hackers and security experts specializes in identifying vulnerabilities across enterprise IT infrastructure, mobile applications, and IoT environments. Cyberops is known for delivering tailored security solutions that strengthen organizational defenses.
3. Hicube Infosec
Hicube Infosec is a well-established cybersecurity company offering penetration testing, risk assessment, and incident response services. Leveraging advanced security tools and experienced professionals, the company focuses on network security, data protection, and compliance management.
4. eSec Forte
eSec Forte is a recognized name in VAPT and cybersecurity consulting, offering a comprehensive approach to security assessments. Their services include application security, infrastructure security, and compliance consulting. The company serves large enterprises, government agencies, and financial institutions.
5. Isecurion
Isecurion specializes in penetration testing and digital forensics, providing customized security solutions. Their strengths include offensive security testing, cloud security assessments, and security policy implementation, helping organizations proactively address cyber threats.
6. Suma Soft
Suma Soft offers VAPT services along with managed security solutions. With a strong focus on network security, endpoint protection, and incident response, the company brings over two decades of IT services experience to deliver reliable long-term security solutions.
7. Protiviti India
Protiviti is a global consulting firm with a strong presence in India, offering comprehensive VAPT and cybersecurity services. Their risk-based approach helps organizations manage threats related to cyberattacks, data breaches, and regulatory compliance.
8. Cryptus Cyber Security
Cryptus Cyber Security is a well-known cybersecurity training and service provider specializing in penetration testing, ethical hacking, and cyber defense. The company serves startups, enterprises, and government organizations by securing digital assets through detailed security assessments.
9. Indian Cyber Security Solutions (ICSS)
ICSS provides cost-effective yet high-quality VAPT services. Their offerings include web application testing, network security audits, and cloud security assessments, along with cybersecurity training programs to promote best security practices.
10. Secugenius
Secugenius delivers penetration testing, vulnerability management, and cyber risk consulting services. Their solutions are tailored for industries such as finance, healthcare, and e-commerce, ensuring protection against evolving cyber threats.
Why VAPT?
Vulnerability Assessment and Penetration Testing is essential for safeguarding IT infrastructure and digital assets.
Identifying weaknesses before attackers exploit them
Managing and prioritizing security risks
Meeting compliance requirements such as ISO 27001, PCI DSS, and GDPR
Protecting sensitive customer, financial, and proprietary data
Preventing exploitation through proactive security measures
Building trust with clients and business partners
Avoiding financial losses caused by cyber incidents
Understanding VAPT: Components and Benefits
VAPT consists of two core components: Vulnerability Assessment (VA) and Penetration Testing (PT).
Vulnerability Assessment (VA)
This process uses automated tools to scan systems and identify security weaknesses. The objective is to generate a detailed list of vulnerabilities that could potentially be exploited.
Penetration Testing (PT)
Penetration testing, also known as ethical hacking, is a manual process where security professionals simulate real-world attacks to exploit vulnerabilities and assess their impact.
Together, VA and PT help organizations identify security flaws and understand their risk exposure.
Best VAPT in India: Elevate Your Security with Cyber Security Hive
Cyber Security Hive stands out as one of India’s leading VAPT providers, offering customized and comprehensive security solutions.
Holistic vulnerability assessments using advanced tools
Real-world penetration testing conducted by certified ethical hackers
Risk mitigation strategies to strengthen security posture
Compliance assurance for standards such as ISO 27001, SOC 2, and PCI DSS
Incident response and business continuity planning
Continuous security monitoring for proactive threat detection
Certification Services
Cyber Security Hive also supports organizations with security and compliance certifications.
ISO 27001 Certification for information security management
SOC 2 Compliance for data protection and operational integrity
PCI DSS Certification for secure payment card processing
HIPAA Compliance for healthcare data protection
GDPR Compliance for European data protection requirements
With cyber threats increasing in scale and sophistication, selecting the right VAPT company is critical for maintaining strong security. The companies listed above provide advanced cybersecurity solutions for organizations of all sizes, covering penetration testing, risk assessment, and compliance assurance.
Cyber Security Hive continues to lead the industry with expert VAPT services and security consulting, helping businesses strengthen their defenses and stay resilient against cyber threats.
Key Takeaways
VAPT is essential for securing modern IT environments
India is home to top VAPT providers offering advanced security testing
Regular security assessments support compliance and data protection
Choosing the right VAPT partner enhances long-term cybersecurity and risk management
📞 Contact Cyber Security Hive for a free cybersecurity consultation and elevate your organization’s security posture. 🚀