



The trend toward mobile security is rapidly increasing. Most people today own at least one smartphone and often a tablet as well. Many individuals use multiple devices for work and personal purposes. The number of people without mobile devices is steadily declining, as even elderly individuals and young children now use smartphones—often their parents’ devices. It is safe to say that mobile devices have become an inseparable part of daily life.
Mobile phones are no longer just communication tools. They have evolved into lifestyle devices. From online shopping and banking to photography, email, music, messaging, and social media, smartphones are deeply embedded in how we live and work. For many users, the device itself—and its features—has become part of their personal identity.
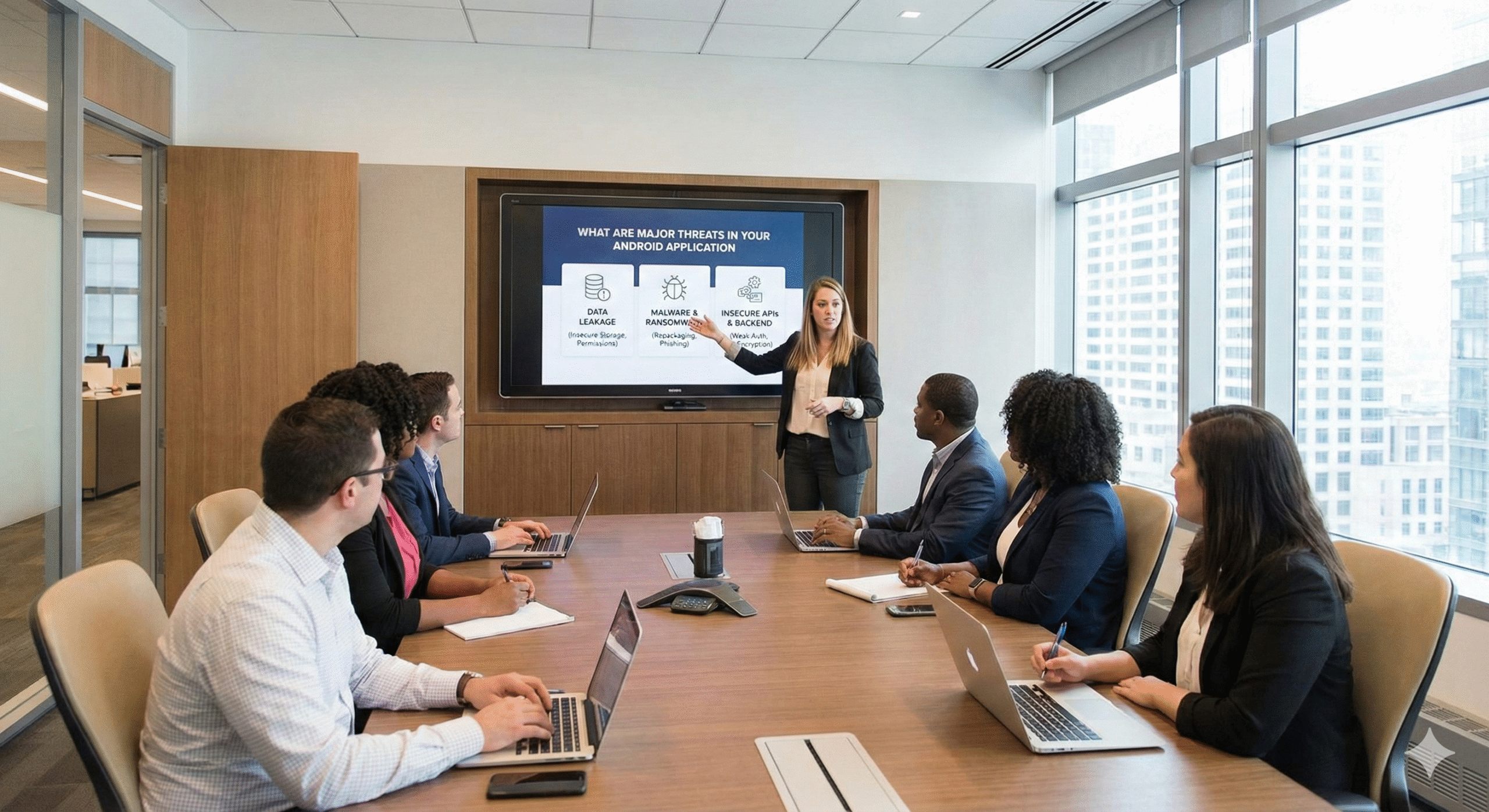
Malware is malicious software embedded within downloadable files that installs itself when a vulnerability is exploited. There is malware specifically designed to target mobile devices, particularly those running on Android. Cybercriminals focus their efforts where users and financial transactions are concentrated—and mobile devices are now a primary gateway to online services.
Although traditional computer viruses are less of a threat to mobile devices, other forms of malware pose serious risks. Some applications exist solely to collect user data while providing little to no legitimate functionality. By accepting terms and conditions, users may unknowingly grant permission for their data to be collected and misused.
Public Wi-Fi networks present significant security risks. Traffic transmitted over unsecured networks is often unencrypted, making it easy for attackers to intercept data. These networks can also be used to distribute malware.
In locations such as coffee shops, airports, and malls, attackers may create fake Wi-Fi access points that appear legitimate. Connecting to these networks can expose your device, login credentials, and sensitive data. This technique is known as network spoofing. Using public Wi-Fi without a VPN should always be considered unsafe.
Data leakage refers to unauthorized access to information without a direct attack. It is one of the most serious mobile security threats today. Mobile devices often contain dozens of applications, many of which request extensive permissions—such as access to microphones, cameras, files, and contacts.
Users frequently store personal data, login credentials, and payment information within apps. Excessive permissions, insecure backend services, or poor data handling practices can lead to data leaks. In some cases, service providers may sell user data for marketing purposes, while attackers may use leaked information for identity theft.
Some applications store sensitive user data locally on devices without adequate protection. While operating systems provide basic encryption, this alone may not be sufficient. Additional layers of encryption and secure hardware features—such as Apple’s Secure Enclave—should be used to protect sensitive data across platforms.
App permissions are intended to act as a security boundary between applications and sensitive phone data, but they are not always enforced effectively. Developers may provide vague or unclear explanations for permission requests.
Users should carefully evaluate whether an app truly requires the permissions it asks for. Applications with extensive access can potentially listen through microphones, access cameras, read SMS messages, or view call logs. Trust in the app and its developer is critical before granting such permissions.
Mobile applications often communicate with backend servers, which are frequent targets for attackers. Security breaches can occur when certificate validation or other server-side controls are disabled—often during development or testing—and never re-enabled.
To identify these risks, applications should always be tested against man-in-the-middle (MITM) attack scenarios to ensure secure communication channels are enforced.
The user plays a critical role in overall mobile security. Even the most advanced security tools cannot fully protect against poor user behavior. Actions such as installing apps from untrusted sources, granting unnecessary permissions, using weak or reused passwords, or falling for phishing scams can severely weaken security.
Mistakes on the internet are easy to make and can happen to anyone. However, adopting good security habits significantly reduces risk.
Security tools such as VPNs, antivirus software, and password managers not only protect against external threats but also reduce the likelihood of user-based errors. Comprehensive solutions like F-Secure TOTAL provide multiple layers of protection to enhance mobile security and safeguard personal data.