



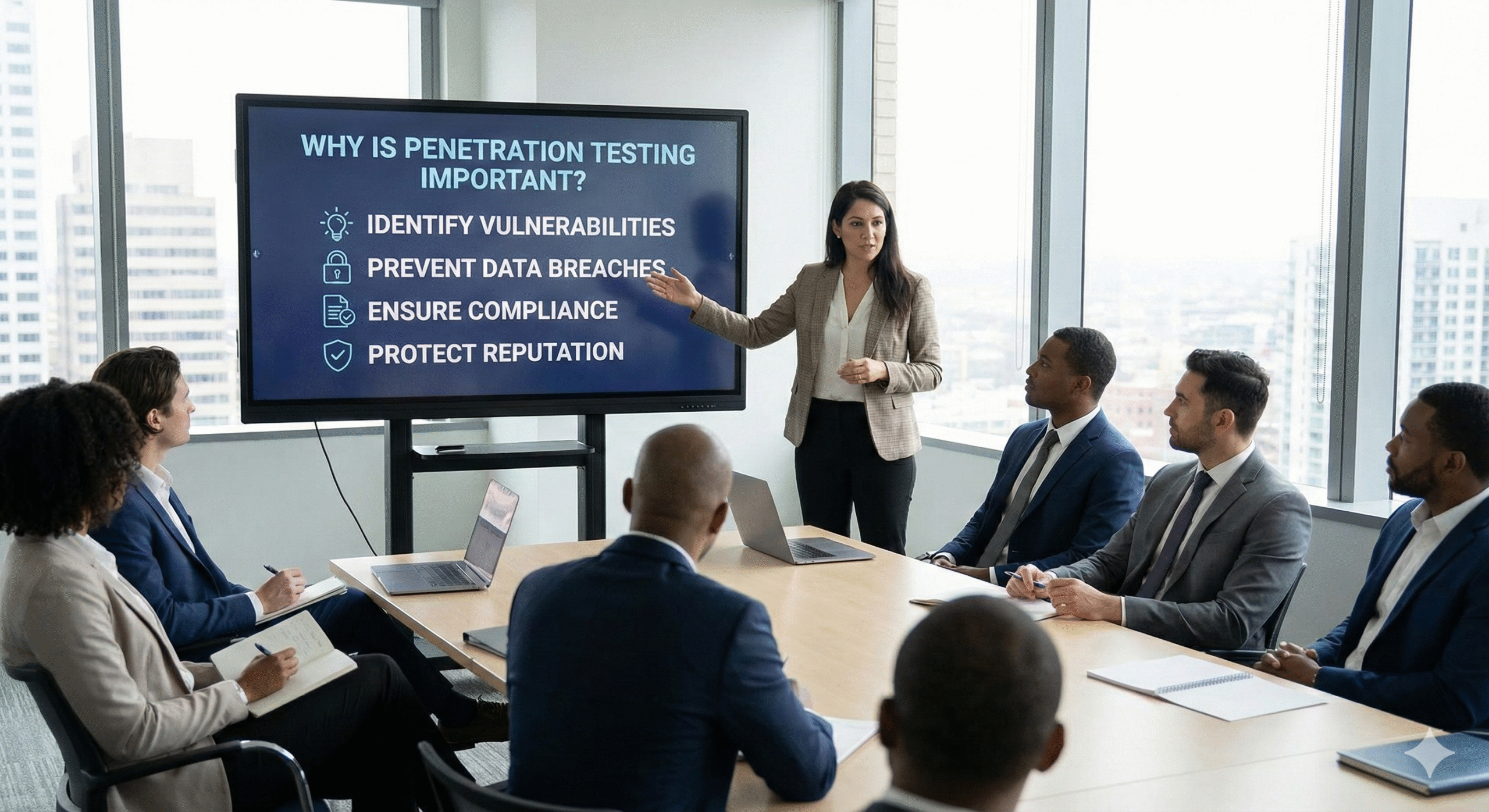
Penetration testing is vital because it helps identify vulnerabilities within your systems before attackers can exploit them. It enables organizations to uncover potential weaknesses and provides a realistic simulation of the challenges faced by cyber defenders, allowing security teams to better prepare for real-world attacks.
Penetration testing also helps identify security gaps in operational processes and ensures that appropriate procedures and policies are in place to protect systems from compromise. However, it is important to note that penetration testing alone cannot confirm the complete security posture of a network environment. Only a full network assessment can provide comprehensive visibility, including evaluations of firewalls, intrusion detection systems (IDS), antivirus solutions, and other security controls. Penetration testing is most effective when conducted alongside a thorough network assessment.
Penetration testing plays a critical role in reducing the financial and operational impact of successful security breaches. When a data breach occurs, costs related to containment, recovery, regulatory fines, legal exposure, and reputational damage can escalate rapidly. Extended business disruption can also result in significant revenue losses due to delayed or inaccurate service delivery.
In severe cases, cyber incidents can be catastrophic, threatening business continuity and long-standing organizational legacies. One of the most dangerous scenarios is when unknown vulnerabilities exist while leadership assumes systems are secure. This false sense of security leads to reduced vigilance, allowing attackers to probe assets unnoticed. In many cases, successful breaches remain undetected for months.
Another key reason penetration testing is important is that it provides measurable feedback on the effectiveness of deployed security tools. Organizations commonly rely on antivirus software, backup solutions, anti-malware services, and system monitoring tools. While leadership may assume these tools are effective, their real-world performance cannot be verified without proper testing.
Penetration testing also helps identify misconfigurations and default settings. These common oversights can allow attackers to bypass or disable security controls, increasing the likelihood of a successful attack and resulting financial losses.
A secure infrastructure is essential for any organization. Penetration testing is one of the most effective ways to evaluate security controls by identifying weaknesses in applications and networks that could be exploited by cybercriminals.
Zero-day threats arise when attackers discover new vulnerabilities before developers can release fixes. Regular and continuous penetration testing helps identify these risks early and block attacker access before vulnerabilities are exploited.
Deploying new applications or infrastructure is necessary for business growth, but it can also introduce new security risks. Point-in-time penetration tests help ensure that new services do not weaken the organization’s overall security posture.
Protecting organizational data is critical, as threats may come from external attackers or internal actors such as compromised employees. Penetration testing is a non-destructive way to identify potential security gaps before an attack occurs, improving readiness and awareness.
Organizations are often required to demonstrate due diligence by proving they have taken reasonable steps to mitigate cybersecurity risks. Penetration testing is especially important in third-party agreements, audits, and corporate acquisitions, where security assurance is essential.
Many industries and government agencies require formal risk assessments. Regular penetration testing supports these requirements and aligns with standards such as NIST 800-30 and ISO 27005, helping organizations meet regulatory expectations.
Penetration testing is essential for meeting compliance requirements across various regulations and standards, including PCI DSS, HIPAA, GDPR, and CCPA. Regular and documented penetration testing provides an auditable trail of security assessments, which is critical in the event of a cyber incident.
By incorporating penetration testing into a broader security strategy, organizations can proactively reduce risk, validate defenses, and maintain compliance in an increasingly complex threat landscape.