



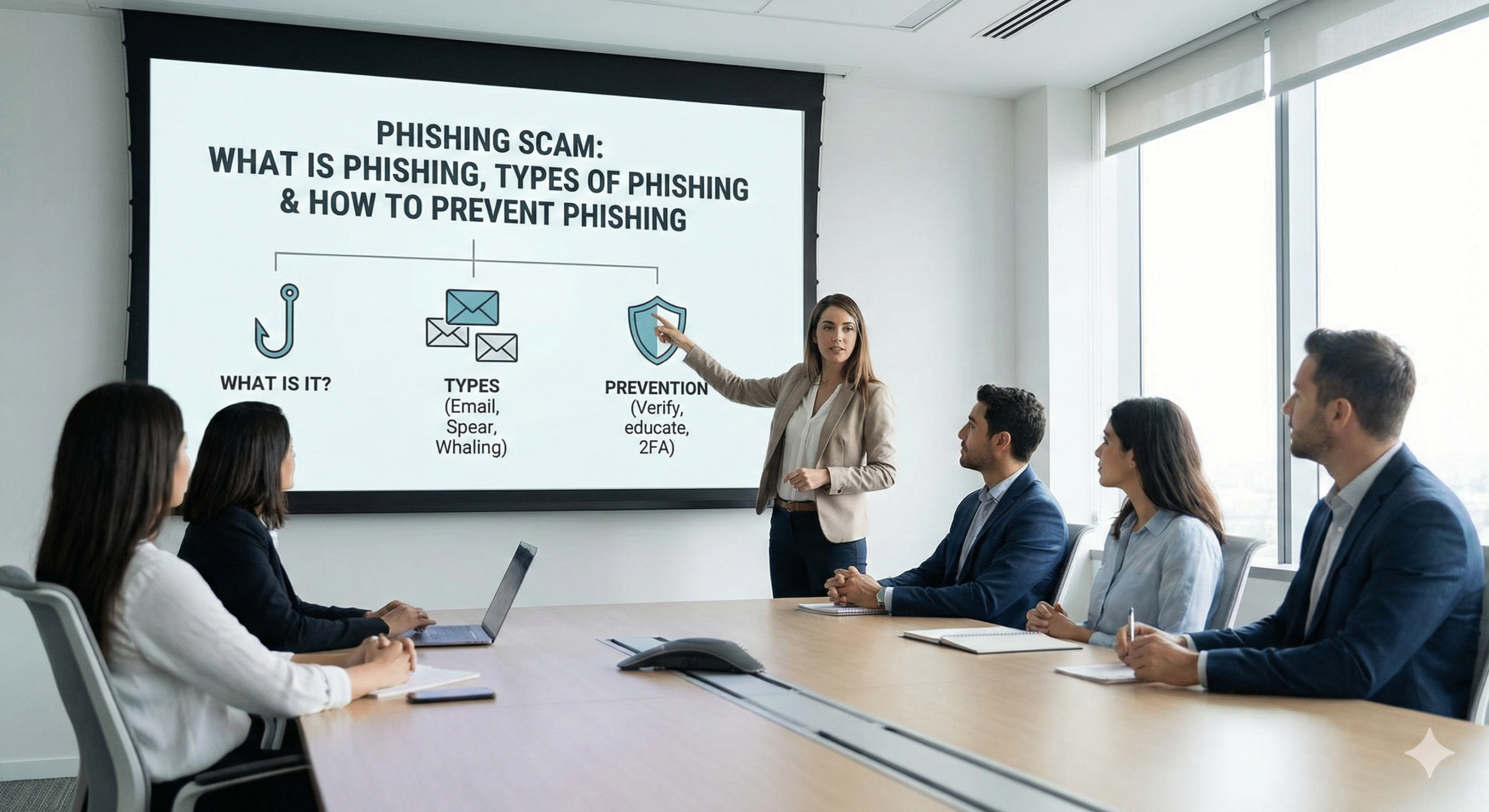
The term phishing is derived from the word fishing, referring to attackers “casting a bait” in the hope that users will take the bite. Cybercriminals attempt to trick individuals into sharing sensitive information such as credit card numbers, bank details, usernames, passwords, or other valuable data by using fake yet legitimate-looking emails, websites, advertisements, or messages.
Phishing is a form of social engineering attack commonly used to steal user data, including login credentials and financial information. In a typical phishing attack, the attacker impersonates a trusted entity and deceives the victim into opening an email, text message, or instant message. The victim is then encouraged to click a malicious link or download an attachment, which may lead to malware installation, ransomware attacks, system compromise, or data theft.
Phishing is often used as an entry point for larger cyberattacks, such as Advanced Persistent Threats (APTs). In these cases, attackers compromise employees to bypass security controls, spread malware within internal networks, or gain unauthorized access to sensitive systems and data.
This is the most common form of phishing. Attackers send emails that appear to be from legitimate organizations, attempting to trick recipients into revealing sensitive information.
Malware phishing encourages victims to click on malicious links or download infected attachments, resulting in malware being installed on their devices. This is currently one of the most prevalent phishing techniques.
Spear phishing is a highly targeted attack aimed at specific individuals such as executives, public figures, or high-value targets. These attacks are carefully researched and personalized.
Smishing uses SMS or text messages to deliver malicious links to smartphone users. These messages often appear as account alerts, prize notifications, or urgent updates.
In this attack, cybercriminals create fraudulent websites designed to steal personal data or payments. These sites may appear in search engine results or as paid advertisements for popular keywords.
Vishing, or voice phishing, involves attackers calling victims while pretending to be from trusted organizations such as banks, government agencies, or technical support teams to extract sensitive information.
Pharming, also known as DNS poisoning, is a sophisticated phishing technique that redirects users from legitimate websites to fake ones without their knowledge, often to steal credentials or financial information.
Clone phishing occurs when attackers compromise an email account and modify a legitimate email by replacing links or attachments with malicious ones, then send it to the victim’s contacts to spread the attack.
Avoid clicking on links in emails or messages, even if they appear to come from known senders. Always hover over links to verify the destination URL. Sophisticated phishing attacks can closely mimic legitimate websites to capture keystrokes or steal credentials.
Multi-factor authentication adds an extra layer of security by requiring a secondary verification step, such as a one-time code sent to your phone. This significantly reduces the risk of account compromise.
Password managers securely store credentials and reduce the risk of password reuse or exposure. They also help prevent users from entering credentials on fake websites.
Using a Virtual Private Network (VPN) encrypts your internet traffic and hides your location, making it harder for attackers to intercept or monitor online activities.
Regularly update your operating system and web browsers. Security updates often contain patches for newly discovered vulnerabilities that attackers could exploit.
Organizations must regularly conduct security awareness training to combat phishing threats effectively. Repeated training helps employees recognize suspicious messages and develop secure habits, making threat detection second nature.
Companies can use Cyber Security Hive’s phishing simulation services to measure their organization’s phishing susceptibility rate. Once the phishing rate is identified, a cloud-based security awareness training program can be implemented.
A second round of phishing simulations typically demonstrates measurable improvement in an organization’s cybersecurity posture and a significant reduction in phishing success rates.