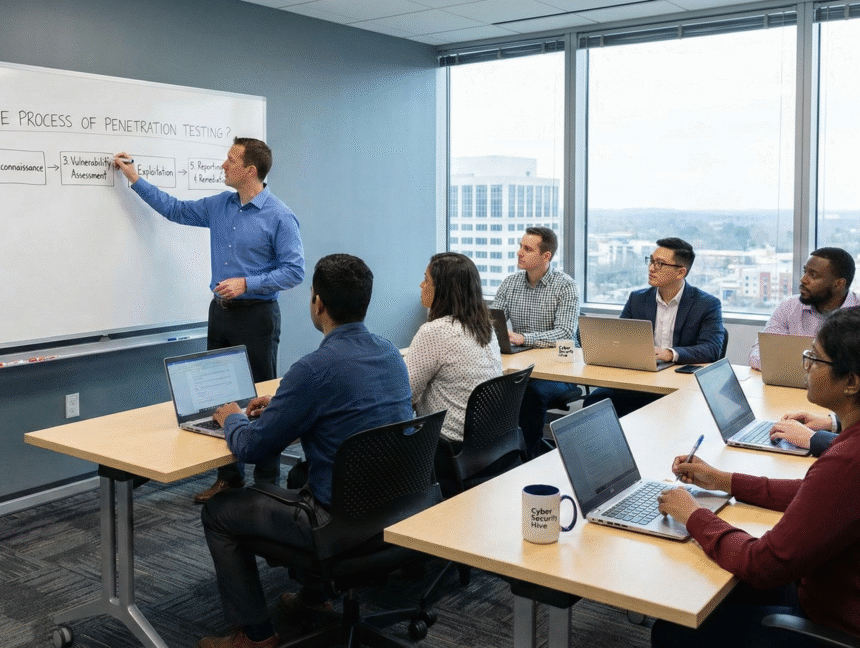
Penetration Testing
A penetration test, commonly known as a pen test, is an authorized and controlled attempt to evaluate the security of an IT infrastructure by safely exploiting vulnerabilities. These vulnerabilities may exist in operating systems, services, applications, misconfigurations, or risky end-user behavior.